
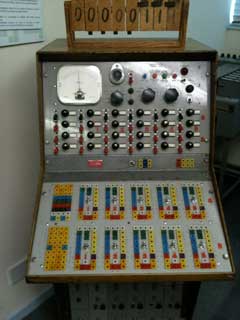

These photo's were taken on October 28th 2010 at The National Museum of Computing at Bletchley Park, one-time home of mathematician/codebreaker Alan Turing. 2012 marked Turing's 1st Centennial.
My blog is at blog.cyberwar.nl.
My RSS aggregator is at news.cyberwar.nl.
An archive of documents obtained from the public internet is kept at cyberwar.nl/d/ (because links break all too often and Lots Of Copies Keep Stuff Safe).
phibetaiota.net | lightbluetouchpaper.org | emergentchaos.com | schneier.com | shmoo.com | taosecurity.blogspot.com | conspicuouschatter.wordpress.com | blog.didierstevens.com | educatedguesswork.org | tscm.com | osvdb.org | exploit-db.com
Headlines (past week) | Full Disclosure | DailyDave | Securiteam | Risks Digest | Crypto-Gram | EDRI-gram | Cipher - IEEE Security & Privacy

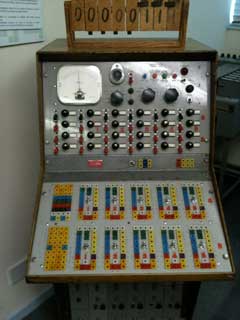

These photo's were taken on October 28th 2010 at The National Museum of Computing at Bletchley Park, one-time home of mathematician/codebreaker Alan Turing. 2012 marked Turing's 1st Centennial.
Last update: 2025-07-26 19:32:54.
Author: Matthijs R. Koot, or whoever you wish... I mean really, why would you trust this webpage to contain accurate claims? On the Internet one should ALWAYS question information. Be a productive skeptic!